The web is full of articles stressing the importance of website security and how you should not compromise on it. A website that asks customers for sensitive data such as their credit card information and passwords for login forms should be totally secured with SSL certificates (now TLS). But in the process, many website owners compromise on their site’s performance.
A slow-loading website is a bane. You cannot have a website that is foolproof yet takes 3 or more seconds to load. It’s come to our notice that netizens don’t hang around for more than 3 seconds for a website to load! So what can you do to improve your security but not let your user experience deteriorate at the same time?! We have just the right answers!
But first, what is TLS? And how is it different from SSL?
TLS stands for Transport Layer Security. It has been used interchangeably with SSL since TLS grew out of SSL. TLS is the successor to SSL and is considered much safer since it does a better job of addressing vulnerabilities that its previous versions couldn’t. Here, we’ll be talking about certain features of TLS that hinder website performance and how you can overcome them.
1. Optimizing the TLS record
TLS encrypts the data exchanged between a web browser and server and authenticates them to prevent eavesdropping and tampering. It is used for open networks pretty widely.
In the first step, the browser encrypts the data using TLS and the server decrypts it. It also works the other way round when the flow of data reverses. This encryption/decryption is also called the TLS record and it constitutes half the workload of TLS. (The rest half is covered by the TLS handshake which we’ll look at optimizing later). This encryption/decryption process has to work for your entire website and swallows up a chunk of time.
There are several ciphers used to perform the TLS record, namely RC4, Camellia, 3DES, AES, etc. AES (Advanced Encryption Standard) is the most popular cipher chosen to protect confidential information in different hardware and software in recent times.
You can play this to your advantage in order to establish a fast and secure connection. However, you should configure your CPU to support AES.
2. Optimizing the TLS handshake
The authenticity of the server and client are established using a process called the TLS handshake. A TLS handshake protocol includes:
- Negotiation of the cipher to be used between the client and server
- Authentication of the identity of server and client using public/private key pairs
- Exchange of pre-master secret and keys to start encrypting data
- Exchange of information
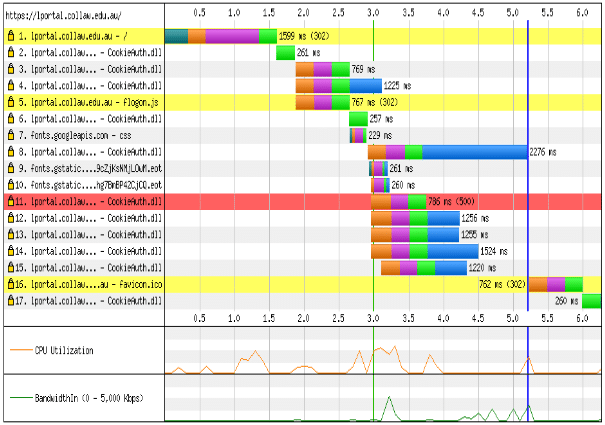
An average TLS handshake is found to take a quarter second to half a second. Take a look at the diagram above and you’ll notice the time at which the handshake protocol occurs. The protocol is delaying the browser from getting to the HTML page.
Moreover, the browser cannot use this time to download any CSS files or images. This is the primary reason why a TLS handshake reduces site performance. In comparison with an unencrypted connection, a TLS encrypted one takes twice the time to load a page. So how do you optimize this process? Here’s what you can do.
- Aim to optimize the certificate chain length. Browsers consist of a list of certificates they trust. A browser connected to you will first look to authenticate your website by looking at your certificate and if it doesn’t trust it, it’ll look for the next certificate in your chain. The sooner it finds a certificate it trusts, the lesser the time lag.
- Get your intermediate certificates bundled with your site’s digital certificate. This limits the time taken by the browser searching for and downloading certificates before it finds one it trusts.
3. Think before you choose plugins
WordPress-enabled websites have lots of plugins available. Though these plugins all provide enriching user experience, it can hurt to have too many. Like the proverb, too many cooks spoil the broth.
Also, if you don’t do a background check on the plugins you install, you wouldn’t know which ones have security vulnerabilities. Having too many plugins leaves you with little time to check for the security of each. It is highly recommended to minimize the number of plugins you use and keep the ones you have updated.
4. Use CAPTCHA!!!
As a user, it’s a frustrating couple of seconds verifying that you’re a human and not a bot. But if you already have this feature on your website and have been thinking of scrapping it, DON’T!!
CAPTCHA is more useful than it seems. It’s a tried and tested method of keeping spambots at bay since it’s quite difficult for bots and malicious software to clear this Turing test. You can also try ReCAPTCHA, which is essentially CAPTCHA modified to include old newspapers and books after digitizing them!
Use a form analytics tool like Formisimo to help you understand the conversion rates with and without CAPTCHA on your forms.
5. Use the best-suited web hosting provider
The security of your website depends a lot on your hosting provider. Do they provide good disk space and bandwidth? Email services? Firewalls?
How about the pricing? Is it worth it?
If your web host does not provide a plan tailor-made for your needs, it’s not worth it. You should consider switching to a different host who can do a better job. Check out this link if you’re considering other web hosts.
Read also: Best Web Hosting Providers in 2020
6. Backup your data
Setup frequent backups for your data. Some web hosts can do this for you. You only need to specify how often it needs to be done. You may also do a manual backup as and when you deem it necessary.
Backing up your data can prevent you from succumbing in case of a security breach or if your server crashes. Backups also come in handy in case of natural disasters.
Lastly, backups are important to nurture a good relationship with your clients. It denotes that you value their information.
Conclusion
With Google favoring websites that use TLS in its search rankings, the fight for ranking on the first page just got more intense. By following the above techniques, you can increase your site’s security while not sacrificing usability.
